
Have you ever searched How to hack smartphones remotely? or How hackers completely take over devices. Checkpoint researchers have shared a critical Instagram vulnerability that could allow hackers to completely take over a device by sending a specially crafted image.
The hacker can also read private messages, delete or post photos but can also execute arbitrary code on the victim’s device.
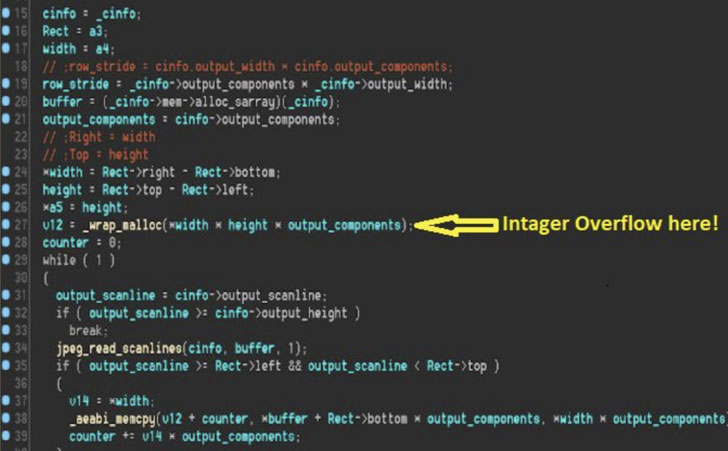
In the advisory published by Facebook, the vulnerability can be tracked as CVE-2020-1895 and was a heap overflow could occur in Instagram for Android when attempting to upload an image with specially crafted dimensions and affects the versions prior to 128.0.0.26.128.
In the blog post Checkpoint, researchers mentioned that hackers can turn the targeted phone into a perfect spying tool that will put the privacy of millions of users at risk.
Researchers found a critical RCE vulnerability in the Instagram app that could allow an attacker to perform any action they wish in the Instagram app.
An attacker just needs to send a specially crafted image via email, WhatsApp or other media when the users save the image in their device after that whenever the user open the Instagram app the flaw is exploited and the attacker gets full access to any resource in the phone.
Since Instagram uses a wide range of permissions including the user’s camera, contacts, GPS, photo library, and microphone an attacker can exploit the flaw and use it for malicious extent.
The Instagram vulnerability was present due to a third party library MozJPEG – an open-source JPEG encoder library which aims to lower bandwidth and provide better compression for images.
However, the Instagram vulnerability was patched six months ago the report was delayed so that maximum users apply the patch and the risk of exploitation is removed.







