
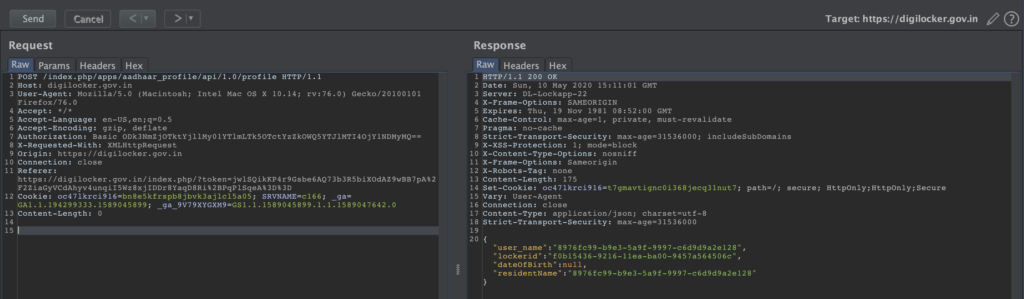
A new critical vulnerability has been found in secure document wallet service Digilocker that could allow an attacker to bypass mobile one-time passwords (OTP) verification and sign in to steal sensitive data.
DigiLocker is a cloud-based national Digital Locker System launched by Govt. of India to store sensitive data such as driving license, vehicle registration, academic mark sheet in digital format.
The OTP function lacks authorization which makes it possible to perform OTP validation with submitting any valid users details and then manipulation flow to sign in as a totally different user
security researcher Mohesh Mohan said
DigiLocker has over 38 million registered users.
DigiLocker OTP Bypass Vulnerability
Mohan said that an attacker can access the DigiLocker of the victim Aadhaar ID or linked mobile number or username prompting the service to send OTP and bypass the flaw in the sign-in process.
The mobile version of the DigiLocker comes with a 4-digit PIN verification in order to add an extra layer of security but the attacker was able to modify the API calls and authenticate the PIN by associating the PIN to another user and successfully logged in as the victim.
You can do the SMS OTP [verification] as one user and submit the pin of a second user, and finally, you will end up logging in as the second user
Mohan said
Secret PIN Bypass/Reset
The more worst part comes due to lack in any authorization in API the attacker can reset pin of any user without authentication by submitting the UUID of the user and the new pin.
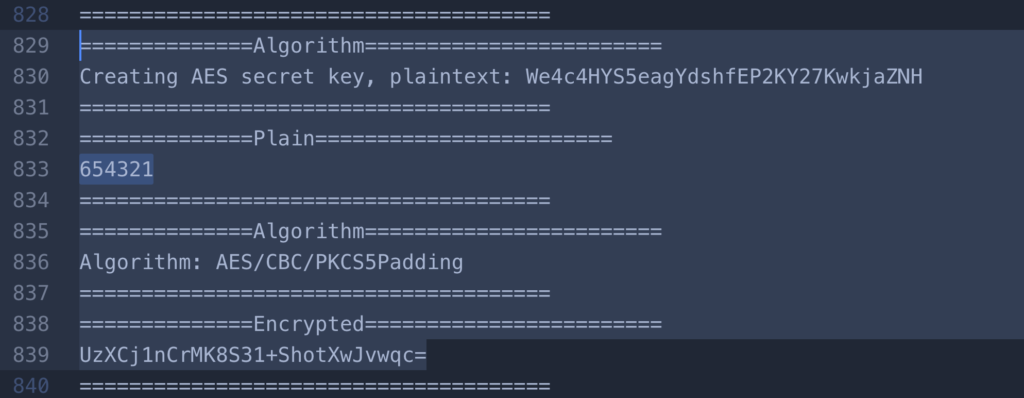
Mohan said that the API calls from mobile were using basic authentication to fetch data or do transactions that can be accessed with removing the is_encrypted: 1. Also, the mobile version was using weak SSL pinning it can be bypass easily with tools like Frida.
It was discovered that this vulnerability had crept in the code when some new features were added recently. The vulnerability was patched on a priority basis by the technical team within a day of getting the alert from CERT-In. This was not an attack on infrastructure, and no data, database, storage, or encryption was compromised
the team added







