
[responsivevoice_button]
In the past few months, Zoom has gained very much popularity, and also Zoom video conferencing has fixed many security flaws that could allow an attacker to perform illegal tasks.
Recently Zoom has also fixed one such flaw that could allow an attacker to crack the numeric passcode of the Zoom private meeting and can snoop on private meetings.
The security flaw was founded by Tom Anthony, VP Product at SearchPilot, he found that initially Zoom meetings were protected with a six-digit numeric password, he witnessed that if an attacker can attempt all 1 Million password in a minute can allow him to crack the password for the private Zoom meeting.
The bug was present due to the lack of Rate limiting. Initially, in April when the Zoom-bombing attacks were increased, Zoom started using passcode for the meetings to stops the Zoom-bombers to spoil the meeting.
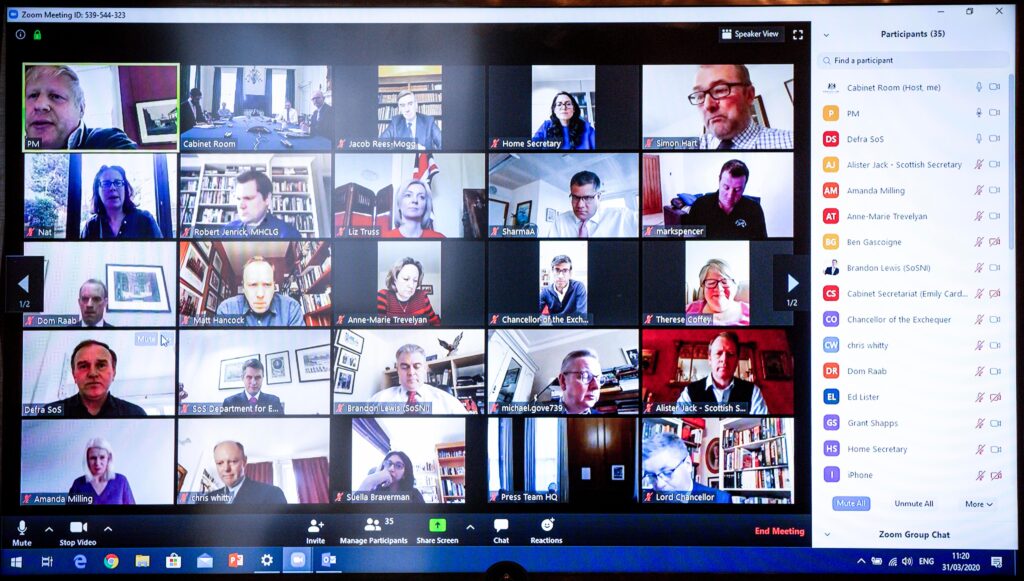
The government has reassured the call was password protected.
Courtesy: Tom Anthony
===FOUND PASSWORD===
Password: 170118
Passwords tried: 43164
took 28m 52s 392ms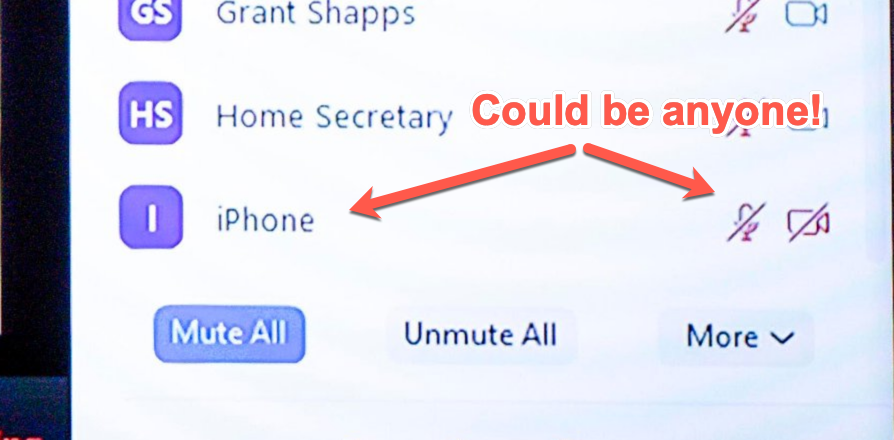
Courtesy: Tom Anthony
After all the Zoom meeting was protected by the six-digit passcode which means that there would be a maximum of 1 Million passcodes but there was no mechanism to check the absence of the repeated number of attempts.
This could allow an attacker to continuously send HTTP requests to try all the one million attempts.
There was a CSRF HTTP header sent during this step, but if you omitted it then the request still seemed to just work fine anyway
Anthony said
The researcher also found that this method also works with scheduled meetings which have the option to override default alphanumeric passcode to try with the top 10 million passcode attempts with brute-force technique.
After finding the flaw the researcher reported it to the company and the patch was released for the security flaw.
The failure on the CSRF token made it even easier to abuse than it would be otherwise, but fixing that wouldn’t provide much protection against this attack
Anthony added
In the past also there have been many flaws found on the Zoom platform earlier this month a zero-day was discovered that could allow an attacker to execute the arbitrary code on the victim’s system.







